

Rebellious, talented and law-abiding twenty-somethings serve as main force in today’s cyber security vigilantism
Countless children dream of becoming a superhero. For many, the dream gradually fades. But others are actually realizing their dreams through invisible battles of good versus evil in the virtual world.
“The word ‘hacker’ has been defamed. It only reminds people of black-hat hackers nowadays, but the term is actually about mutual assistance and chivalry,” 17-year-old Lin Zhihui argued in an interview with the People’s Daily Online.
The pimple-faced teenager currently attends high school in central China’s Jiangxi province. He is shy with his peers, intentionally keeping a low profile. He never plays video games, and fails to muster much enthusiasm for sports.
But on the internet, Lin, who goes by the username of Adrian, is one of the 20 best hackers on China’s leading internet security monitoring platform Butian, where over 30,000 registered white-hat hackers work to detect and mitigate internet vulnerabilities. Unlike black-hat hackers, they hack into protected systems and networks to test and assess the security conditions, avoiding disturbances and participating in no information theft.

(A selfie of Lin Zhihui Photo/Courtesy of Lin Zhihui)
Rebellious but talented
As of March, some 60 percent of white-hat hackers on Butian were born after 1990, and 44 percent of them were born after 1995. Lin, born after 2000, is something of a prodigy. This April, he ranked sixth overall. Since December 2015, he has reported a total of 398 vulnerabilities and taken in a bounty exceeding 43,000 RMB.
Butian’s current top-ranking white-hat hacker of the year goes by the username carry-your. The 25-year-old earns up to 900,000 RMB from vulnerability reports on the platform, according to Yang Yitong, operation officer of Butian.
Yang also recalled that her personal information was promptly exposed when she first took on the job of communicating with the young hackers.
“Now I am more experienced and able to deal with their probes. They are very adorable – funny online, a bit shy offline. But they are all into cool and cutting-edge technologies,” she told the People’s Daily Online.
According to Lin, his first encounter with cyber security was in 2008, when his family bought their first computer.
“I was trying to surf the internet one day, but ended up downloading a virus,” the teenager explained. “My parents were furious. I was ordered to stand in the corner for a whole night as punishment … I wanted to learn how to defend myself [from viruses] after that, and I was concerned that other kids might experience the same punishment.”
Other young hackers admitted that their “epiphany” moments came in more casual, sometimes morally suspect ways. Several said they read novels about cyber wars and hackers, while others tapped into the technology in order to cheat in online games or on social networks. Some credited experiences at internet bars – widely seen as a rendezvous point for rebellious youth – for introducing them to hacker life.
“You just get interested naturally, as to how things function … Learning about technology is so much fun, but not many people understand what you are doing – even my sister, who is a university graduate, doesn’t understand,” a 22-year-old Butian hacker, who asked to be called S, told the People’s Daily Online.
During his adolescence, Lin said he had many quarrels with his parents, especially when his enthusiasm for cyber security caused him to earn lackluster grades at school.
“I ran away from home once. I felt they just did not understand me,” he admitted, adding that he felt more relaxed experimenting with new technologies on vulnerability-testing websites. Lin’s situation at home improved a lot after he used his hacking know-how to locate the thief that stole his family’s cell phone.
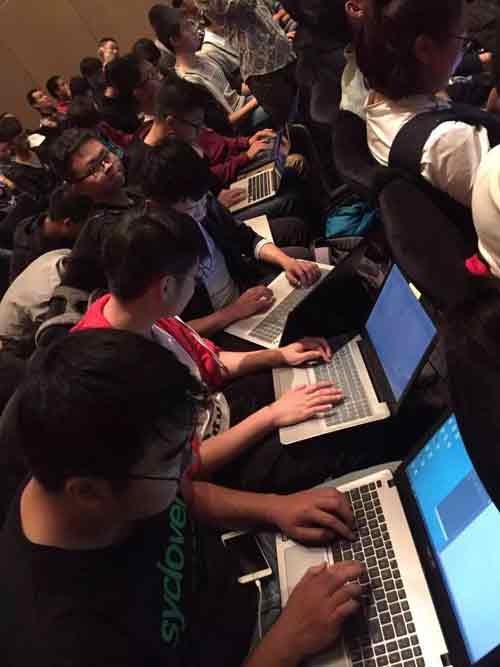
(White hat hackers on a group meeting of Butian Photo/Courtesy of Butian)
Lawful aids
According to a 24-year-old Butian hacker with the username U-Shen, black-hat hackers can earn tens of thousands of RMB per day by selling stolen information. They can get in a day a white-hat hacker might hope to earn in a month. Despite the lure of huge profits, however, the young hackers are firm in their convictions.
“Hacking was originally done for the purpose of achieving balance in technology, and to help others … We need to think like hackers but not act like them,” Lin said.
“It is easy money, but it’s not worth it. You lose everything for one deal. We were repeatedly taught not to cross the line. This is an important rule to protect ourselves,” S noted, adding that Butian offers its hackers regular consultations to enhance their awareness of legal boundaries.
In addition, Butian provides around a dozen group activities for hackers on the platform, including vulnerability detection competitions and campus presentations. These activities aim to build closer community bonds and encourage more participation in vulnerabilities detection, according to Yang.
‘Nation of diligence’
All white-hat hackers are gifted, strong thinkers, said the head of Butian, Bai Jian. Meanwhile, many performed poorly in China’s test-oriented education system, and few on the platform have made it to university.
S is one of those who gave up formal schooling for his cyber security passion. Upon graduating from a vocational school, S immediately sought a job, and has been working at a Shenzhen-based cyber security company for two years. Another hacker, born after 2000, quit high school to work from home for an Australia-based IT company.
“Because they lack higher education, they usually work for smaller IT companies. It is an embarrassing result for real talents left behind by our current education system,” Bai said, adding that some hackers may have weak communication skills, which also makes it harder for them to join bigger enterprises.
But there is hope. This September, Lin is going to the U.K. to study computer science as an undergraduate. The young hacker also harbors the ambition of starting his own cyber security company upon graduation.
“It is gratifying to see China attaching more significance to cyber security. One key problem is that many websites are set up with minimal or outdated maintenance. This becomes a liability once hackers attack. We should be more proactive in cyber security, rather than responding after the fact. I believe, as a diligent nation, we will see a vulnerability-free cyberspace in the future. I hope to one day be out of a job!” the teenage hacker joked.

 Award-winning photos show poverty reduction achievements in NE China's Jilin province
Award-winning photos show poverty reduction achievements in NE China's Jilin province People dance to greet advent of New Year in Ameiqituo Town, Guizhou
People dance to greet advent of New Year in Ameiqituo Town, Guizhou Fire brigade in Shanghai holds group wedding
Fire brigade in Shanghai holds group wedding Tourists enjoy ice sculptures in Datan Town, north China
Tourists enjoy ice sculptures in Datan Town, north China Sunset scenery of Dayan Pagoda in Xi'an
Sunset scenery of Dayan Pagoda in Xi'an Tourists have fun at scenic spot in Nanlong Town, NW China
Tourists have fun at scenic spot in Nanlong Town, NW China Harbin attracts tourists by making best use of ice in winter
Harbin attracts tourists by making best use of ice in winter In pics: FIS Alpine Ski Women's World Cup Slalom
In pics: FIS Alpine Ski Women's World Cup Slalom Black-necked cranes rest at reservoir in Lhunzhub County, Lhasa
Black-necked cranes rest at reservoir in Lhunzhub County, Lhasa China's FAST telescope will be available to foreign scientists in April
China's FAST telescope will be available to foreign scientists in April